Latest Ubiquiti vulnerability #
Earlier this year, Ubiquiti, a popular networking equipment manufacturer for businesses and consumers, disclosed a security breach that potentially exposed customer data. However, recent news indicates that the reported breach was intentionally and severely underreported, and the potential impact was much greater than disclosed. You can read the Krebs article for more in-depth reporting of the breach and its potential impact.
Right now, it's critical to audit and find Ubiquiti devices. After you've identified these devices, consider:
- Changing the passwords and enabling 2FA, if you haven't already.
- Ensuring the devices are on the latest firmware.
- Deleting and rebuilding your device profiles from scratch, if you want to be absolutely certain your systems are not impacted by this breach.
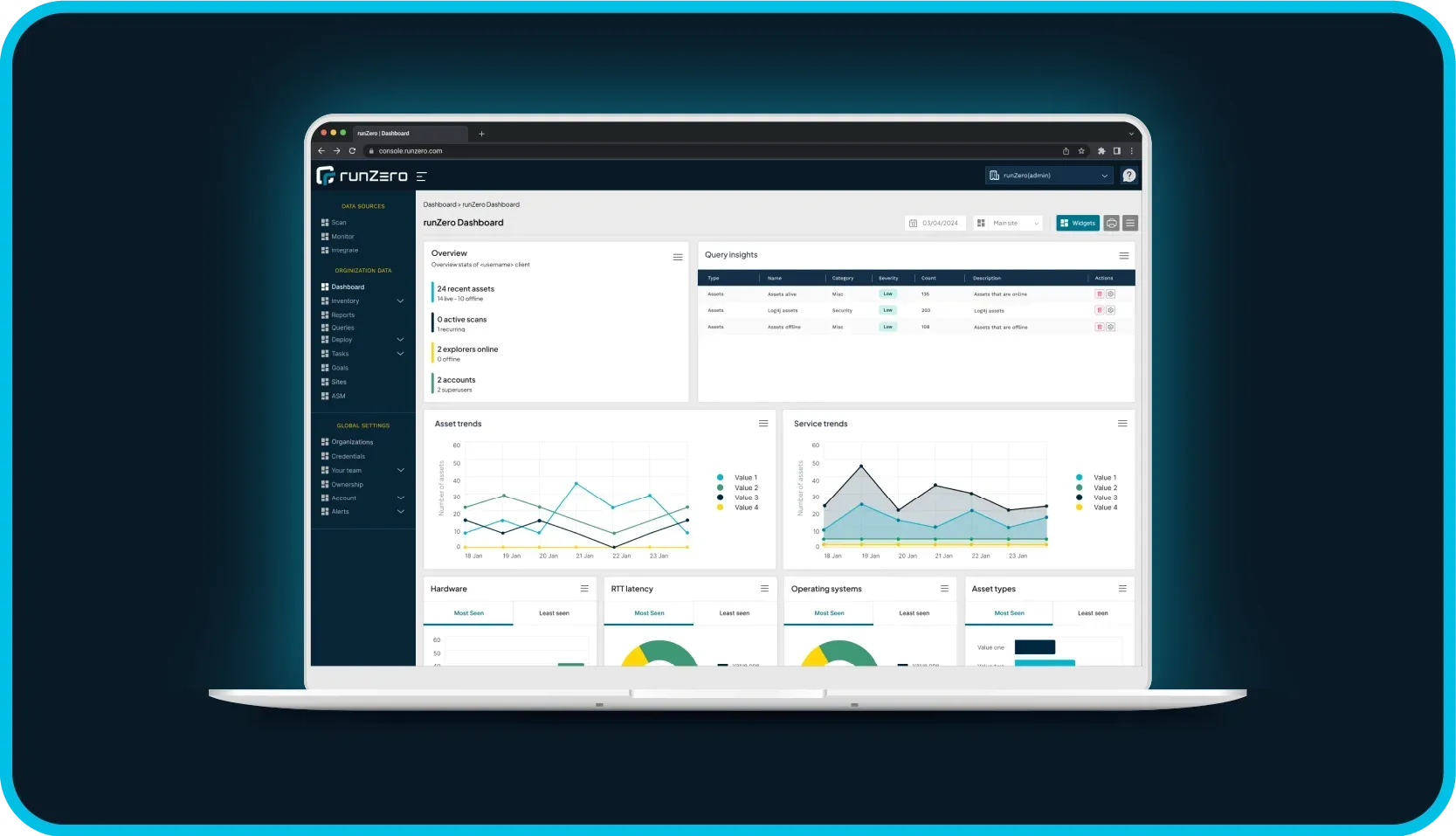
Finding Ubiquiti devices with Rumble #
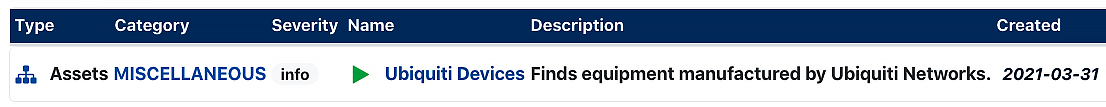
Rumble users can quickly find Ubiquiti devices in their inventory with this handy pre-built query. This query searches for any live asset that has Ubiquiti as the vendor, hardware, or OS, and it also searches for the UBNT protocol.
alive:t AND (vendor:Ubiquiti OR hw:Ubiquiti OR os:Ubiquiti OR protocol:ubnt OR names:unifi OR names:ubiquiti)
As always, any prebuilt queries we create are available from our Queries Library. Check out the library for other useful inventory queries.
Try Rumble #
Don't have Rumble and need help finding Ubiquiti devices? Start your Rumble trial today.