Latest Palo Alto Networks vulnerability #
Palo Alto Networks (PAN) disclosed that certain versions of their PAN-OS software has a vulnerability that allows for remote command injection.
CVE-2024-3400 is rated critical with CVSS score of 9.8 and indicates an unauthenticated attacker can execute arbitrary code with root privileges on the firewall. The vendor indicates that there is evidence of limited exploitation in the wild.
watchTowr has posted a detailed analysis including the details needed for exploitation. This analysis covers two separate vulnerabilities; an arbitrary file creation vulnerability in the session handler, and a shell metacharacter injection issue that leads to remote execution through the telemetry script. PAN has updated their guidance to state that "Disabling device telemetry is no longer an effective mitigation".
What is the impact? #
The following PAN-OS versions are affected by this vulnerability.
Version | Affected | Unaffected |
PAN-OS 11.1 | < 11.1.2-h3 | >= 11.1.2-h3 (hotfix ETA: By 4/14) |
PAN-OS 11.0 | < 11.0.4-h1 | >= 11.0.4-h1 (hotfix ETA: By 4/14) |
PAN-OS 10.2 | < 10.2.9-h1 | >= 10.2.9-h1 (hotfix ETA: By 4/14) |
Palo Alto Networks indicates that PAN-OS 11.1, 11.0, and 10.2 versions with the configurations for both GlobalProtect gateway and device telemetry enabled.
Customers may verify this by checking for entries in the firewall web interface (Network > GlobalProtect > Gateways) and verify whether device telemetry enabled by checking your firewall web interface (Device > Setup > Telemetry).
Are updates or workarounds available? #
Palo Alto Networks recommends that customers with a Threat Prevention subscription can block attacks for this vulnerability by enabling Threat ID 95187 (introduced in Applications and Threats content version 8833-8682) and applying vulnerability protection to GlobalProtect interfaces.
It is also recommended that telemetry be disabled until devices can be upgraded to an unaffected version of PAN-OS.
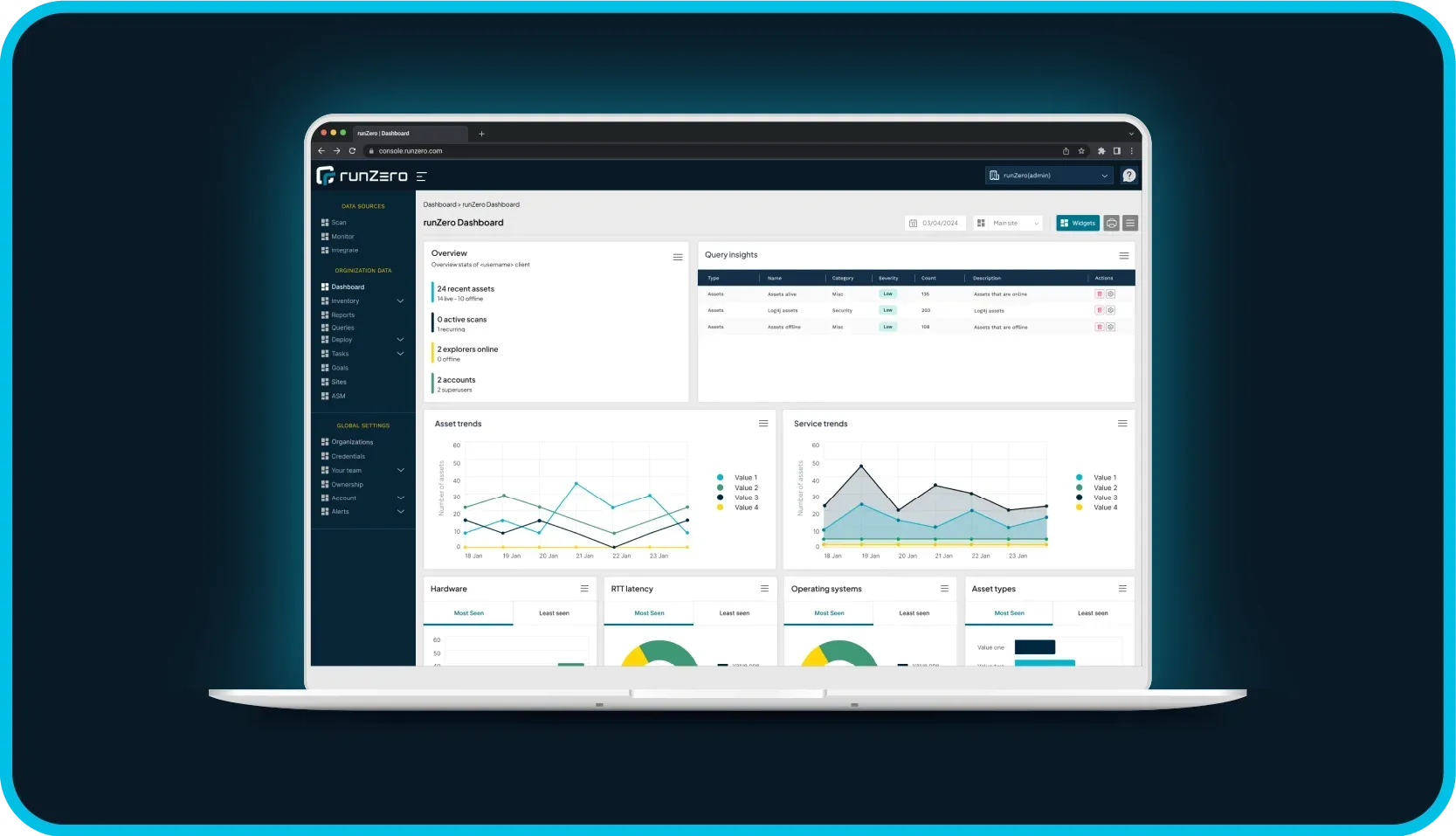
How do I find potentially vulnerable systems with runZero? #
From the Asset Inventory, use the following query to locate systems running potentially vulnerable software:
os:"PAN-OS"