CAASM with its own powerful, proprietary active & passive discovery... not just the same old integrations.
-
Overview
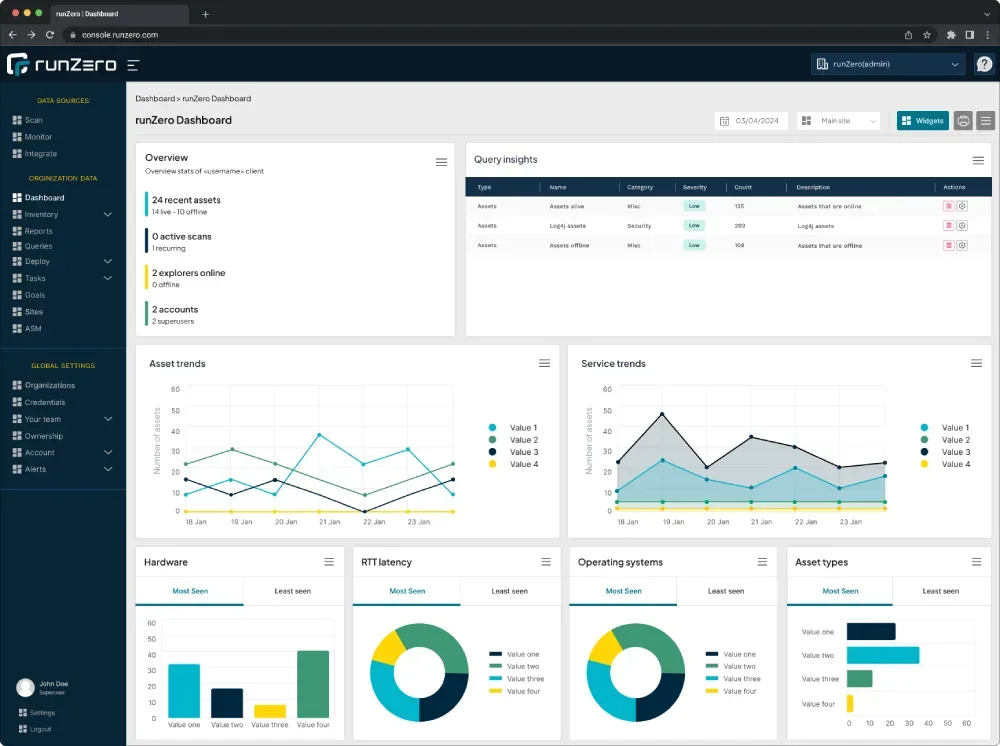
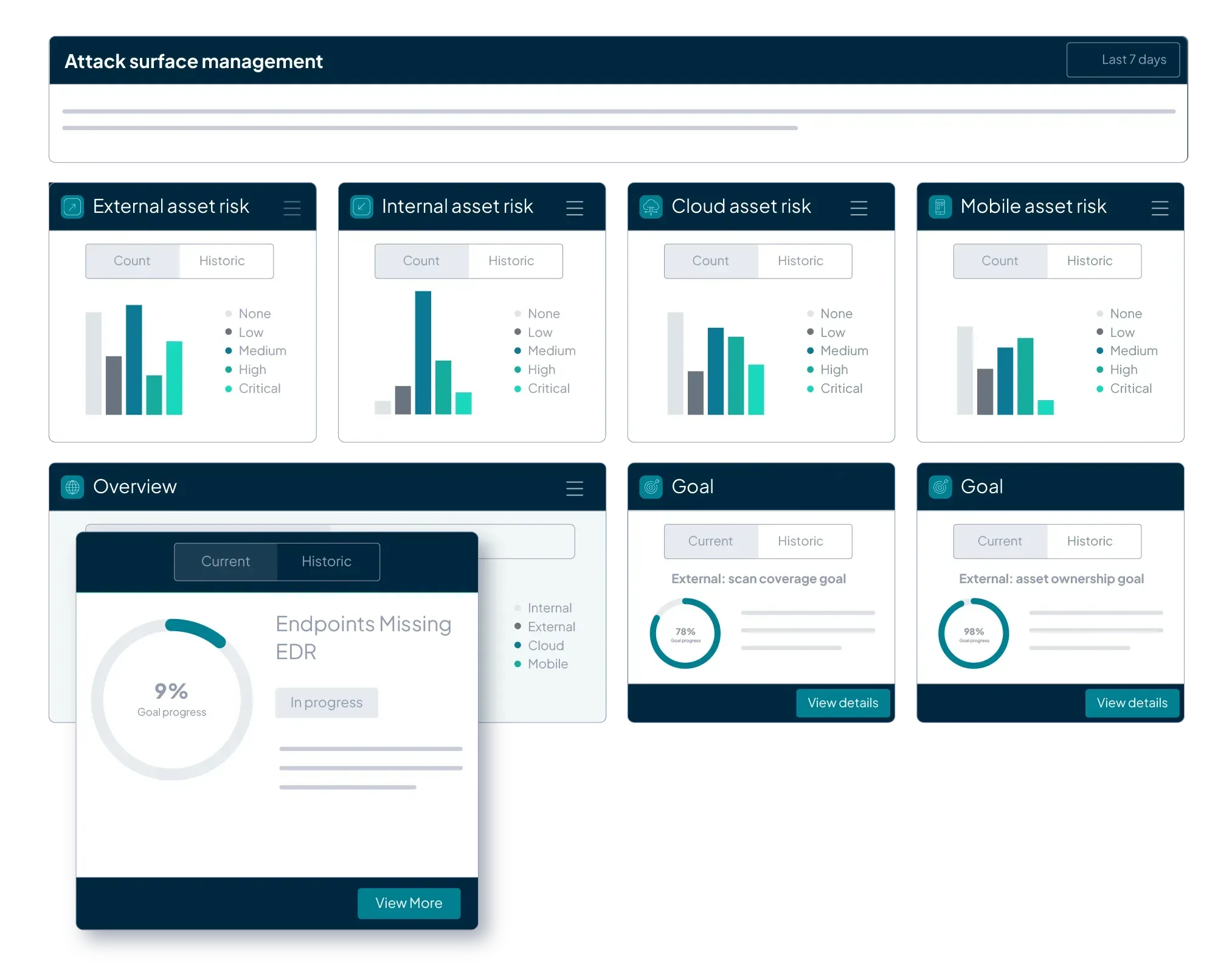
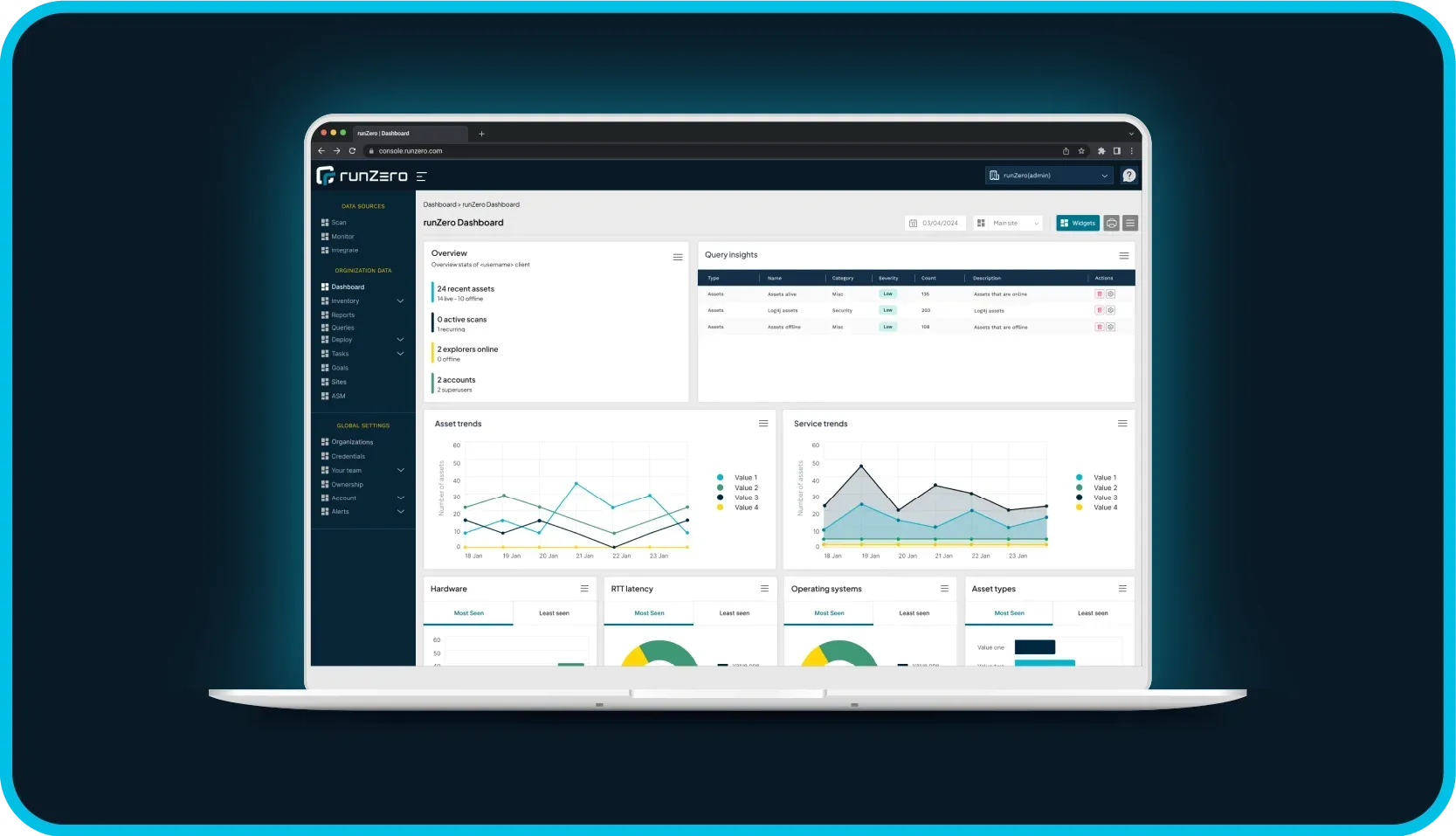
The runZero Platform provides complete security visibility across IT, OT, IoT, cloud, mobile, and remote assets so that you can see and secure everything on your network.
-
Integrations
runZero seamlessly integrates with a wide variety of tools, enhancing network visibility, enriching asset data, and uncovering control gaps.
-
Interactive Demos
Take a deep dive into core features with our interactive demos.
-
Community Edition
Our completely free version of the runZero Platform is ideal for home use and environments with fewer than 100 assets.
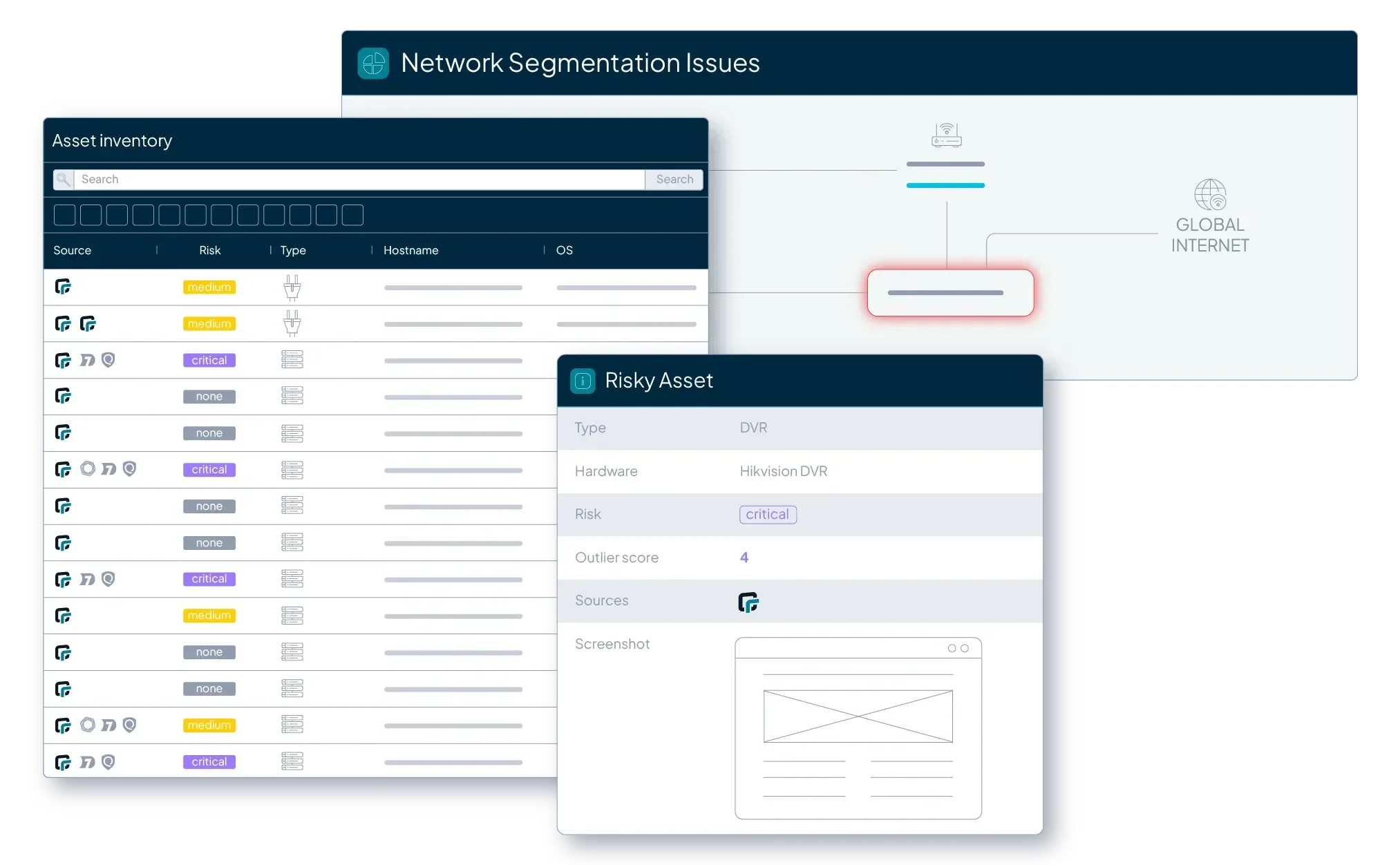
Passive discovery reimagined
The new runZero Platform introduces novel passive discovery perfect for OT & ICS environments.
Explore our latest research, resources, & insights on all things exposure management.
-
runZero Blog
See what's happening at runZero and read up on the latest ideas, opinions, and articles from our experts and researchers.
-
Rapid Response
Respond to 0-day threats immediately with our prebuilt queries and tips from the runZero Research team.
-
Resource Center
Dive into a treasure trove of resources to expand your exposure management knowledge.
-
Support Resources
Everything you need to maximize your experience with the runZero Platform.

Let's connect at RSAC
Meet our team, see what’s new in the Platform, & come relax in our Lounge — located next door to Moscone!
See why the brands you know & love trust runZero.
-
Our Customers
Our customers are everything. We're super proud to be trusted by leading organizations around the globe to help them improve their security.
-
Case Studies
See how runZero has empowered security teams to take control of their networks, uncover their unknowns, and save significant time and money.
-
Testimonials
Read reviews of the runZero Platform and see how teams have improved their security with our technology.

Case Study
York University discovered 2.5x more assets with runZero, enabling them to gain clear visibility and reduce risk in an ever-changing environment.
We're on a mission to create new solutions to solve persistent problems. Let's shake things up.
-
About Us
Wondering who the heck are these people? Meet the team and get the story behind runZero... once upon a time called Rumble.
-
Events
Track down runZero Yetis in the wild! Join us in-person or virtually at one of our upcoming events.
-
Investors
Meet the cybersecurity investors, trailblazers, and innovators who help us navigate our journey and the evolving security landscape.
-
Newsroom
Read the latest articles, announcements, and press releases from runZero.
-
Careers
Want to join our forces? We're looking for bright minds and passionate souls who want to write the next chapter in exposure management.

Life at runZero
Meet the newest rockstar on our squad: Zeti, the runZero Yeti! 🎉 This sub-zero hero is now our official mascot, and we’re excited to give you the lowdown on how Zeti came to be.
Believe customers always come first? Into innovation & the unconventional? We might be great partners.
-
Infinity Partner Program
See how we can work together to provide best-in-class security solutions and outcomes for our joint customers.
-
Trusted Advisor Program
Do you perform project-based consulting services and want to use runZero to deliver great insights? This program is designed for you!
-
Partner Directory
Explore our directory of trusted (and awesome) partners.
-
Partner Login
Login to our Infinity Partner Portal.

Featured Partner
Carahsoft and runZero have joined forces to provide Public Sector customers the solutions they need to secure dynamic attack surfaces.