What are Citrix NetScaler ADCs and Gateways? #
NetScaler Application Delivery Controller (ADC), formerly known as Citrix ADC, acts in a number of capacities to ensure reliable application delivery to users. This can include load balancing across application servers, off-loading of certain operations, security protections, and policy enforcement.
NetScaler Gateway, formerly known as Citrix Gateway, provides single sign-on (SSO) from any device to multiple applications through a single URL.
Latest Citrix vulnerability #
A new vulnerability was disclosed in NetScaler ADC and Gateway products for version 13.1-50.23.
There is currently no associated CVE with this particular vulnerability because Citrix had already disclosed and issue with a previously assigned CVE-2023-4996.
What is the impact? #
The vulnerability would enable an attacker to remotely obtain sensitive information from a NetScaler appliance configured as a Gateway or AAA virtual server via a very commonly connected Web interface, and without requiring authentication. This bug is nearly identical to the Citrix Bleed vulnerability (CVE-2023-4966), except it is less likely to return highly sensitive information to an attacker.
Are updates or workarounds available? #
Citrix recommends customers update to version 13.1-51.15 or later.
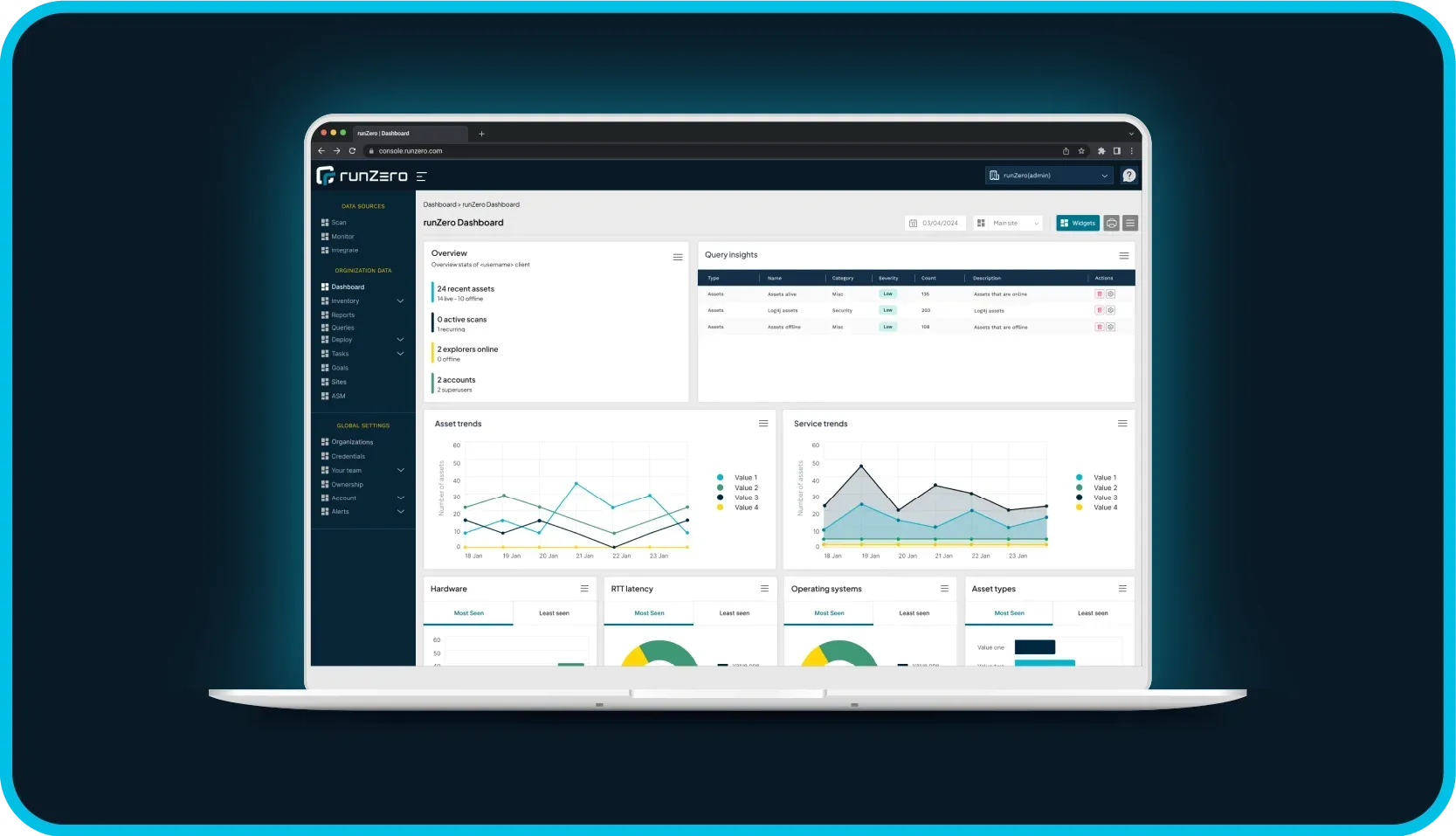
How do I find potentially vulnerable systems with runZero? #
From the Asset Inventory, use the following query to locate systems running potentially vulnerable software:
product:netscalerCVE-2023-3519 (July 2023) #
In July, 2023, Citrix alerted customers to three vulnerabilities in its NetScaler ADC and NetScaler Gateway products. Surfaced by researchers at Resillion, these vulnerabilities included a critical flaw currently being exploited in the wild to give attackers unauthenticated remote code execution on vulnerable NetScaler targets (CVE-2023-3519). Compromised organizations included a critical infrastructure entity in the U.S., where attackers gained access the previous month and successfully exfiltrated Active Directory data. And at the time of publication, there appear to be over 5,000 public-facing vulnerable NetScaler targets.
What was the impact? #
The three reported vulnerabilities affecting NetScaler ADC and Gateway products were of various types, and each include different preconditions required for exploitation:
- Unauthenticated remote code execution (CVE-2023-3519; CVSS score 9.8 - "critical")
- Successful exploitation required the NetScaler target be configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, or RDP Proxy) or "authentication, authorization, and auditing" (AAA) virtual server.
- Reflected cross-site scripting (XSS) (CVE-2023-3466; CVSS score 8.3 - "high")
- Successful exploitation required the victim to be on the same network as the vulnerable NetScaler target when the victim loaded a malicious link (planted by the attacker) in their web browser.
- Privilege escalation to root administrator (nsroot) (CVE-2023-3467; CVSS score 8.0 - "high")
- Successful exploitation required an attacker having achieved command-line access on a vulnerable NetScaler target.
U.S.-based CISA reported attackers exploiting CVE-2023-3519 to install webshells used in further network exploration and data exfiltration, causing CVE-2023-3519 to be added to CISA's Known Exploited Vulnerabilities Catalog. Other common attacker goals, like establishing persistence, lateral movement, and malware deployment, were all potential outcomes following successful exploitation.
Citrix made patched firmware updates available. Admins were advised to update older firmware on vulnerable NetScaler devices as soon as possible.
CISA also made additional information available around indicators of compromise and mitigations.
How did runZero customers find potentially vulnerable NetScaler instances with runZero? #
From the Asset inventory, they used the following prebuilt query to locate NetScaler instances on their network:
hw:netscaler or os:netscaler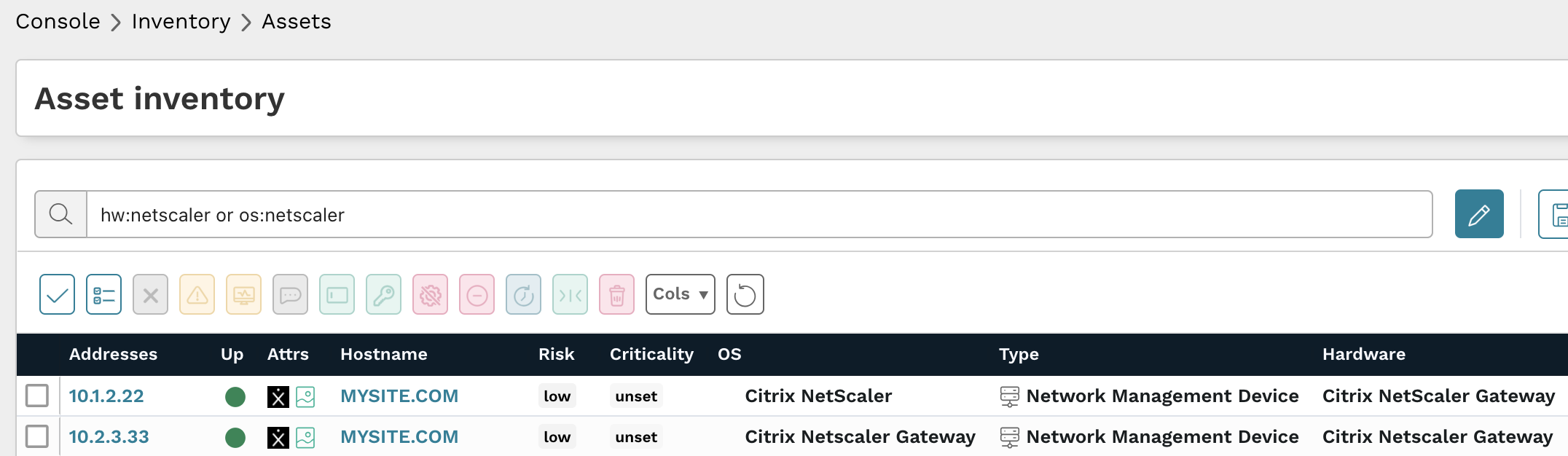
Results from the above query should be triaged to verify they are affected ADC or Gateway products and if they are running updated firmware versions.
The following query could also be used in on the Software and Services inventory pages to locate NetScaler software:
product:netscaler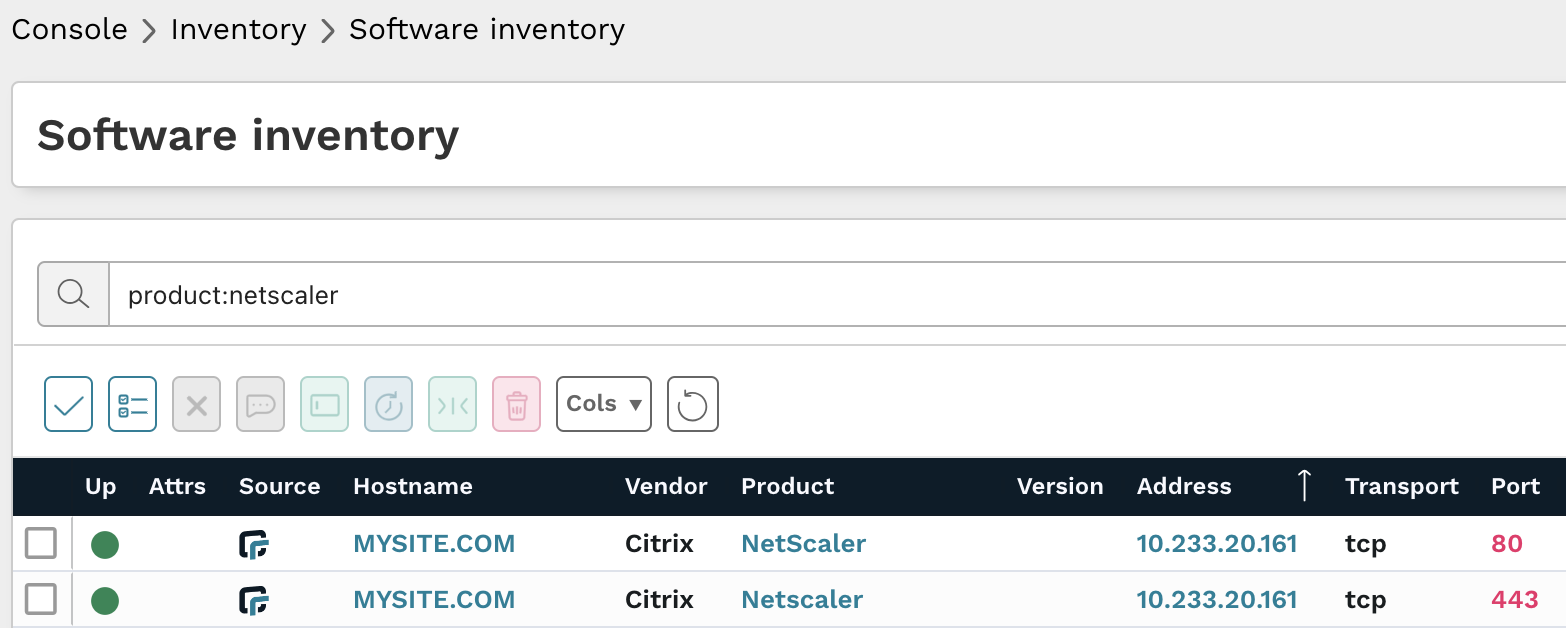
Results from the above query should be triaged to verify they are affected ADC or Gateway products and if they are updated versions.
As always, any prebuilt queries are available from your runZero console. Check out the documentation for other useful inventory queries.