Latest Automation Direct vulnerabilities #
Automation Direct has disclosed multiple vulnerabilities in their C-MORE EA9 HMI product.
CVE-2024-25136 is rated high with CVSS score of 7.5 and allows an attacker to send a relative path in the URL without proper sanitizing.
CVE-2024-25138 is rated medium with a CVSS score of 6.5 and indicates credentials used by the platform are stored as plain text on the device.
CVE-2024-25137 is rated medium with a CVSS score of 4.3 and indicates the program accepts user supplied data that is copied into a fixed stack buffer causing an overflow and leading to denial-of-service conditions.
What is the impact? #
Successful exploitation of these vulnerabilities would allow an attacker to create a denial-of-service condition, or access sensitive resources without authorization.
Are updates or workarounds available? #
Automation Direct recommends that users update C-MORE EA9 HMI to V6.78. Additionally, users should ensure these devices are not accessible from the public internet and ensure they are properly firewalled within business networks and accessible through properly configured VPN software.
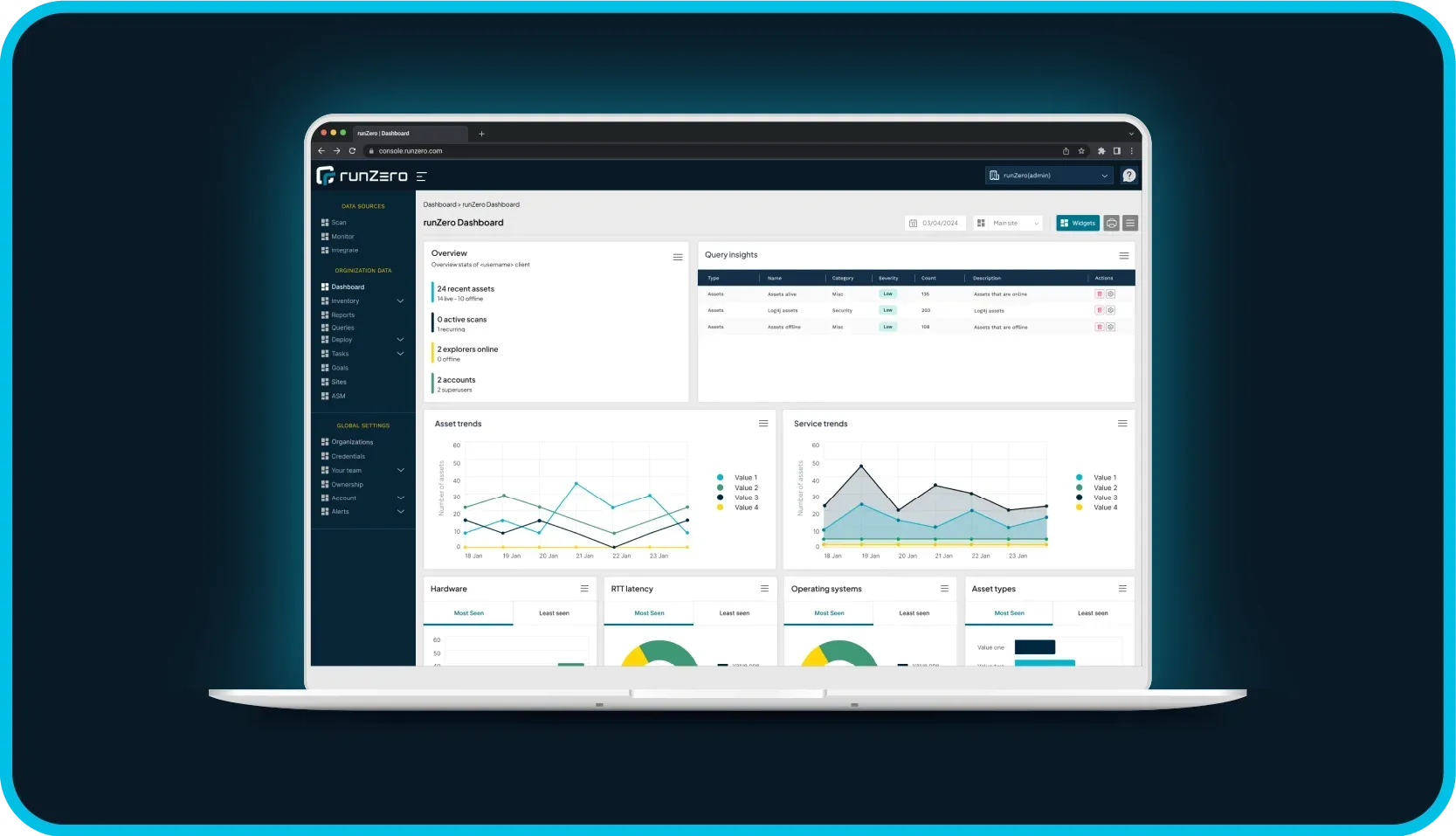
How do I find potentially vulnerable systems with runZero? #
From the Service Inventory, use the following query to locate systems running potentially vulnerable software:
protocol:ftp AND banner:"EA9-"From the Asset Inventory, use the following query to locate systems running potentially vulnerable software:
hw:"C-MORE%"We recommend running both queries to ensure all assets can be identified to take appropriate action.