runZero supports SNMPv1, SNMPv2 (the SNMPv2c variant), and SNMPv3. Watch below to learn more about how runZero works, and discover what's on your network in minutes with a 21-day free trial.
Updated on 2021-10-08: This issue was cited in an excellent paper on SNMP v3 discovery by Taha Albakour, Oliver Gasser, Robert Beverly, and Georgios Smaragdakis. If you are interested in this type of research, please check out our Modern Network Discovery presentation and research blog posts. runZero uses these techniques for device fingerprinting, remote MAC detection, age detection and multi-homed (alias) interface discovery.
Published on 2020-01-03:
Earlier this week, Gerry Gosselin and Eric Rioux of VertitechIT were investigating a strange result in the runZero asset inventory; After scanning an external subnet with runZero, they noticed that the main internet router was responding to SNMP probes on its normal address and HSRP address. The router in question had a strong SNMP v2 community as well an IP ACL on the SNMP service. runZero still reported the router vendor, manufacturing date, and MAC address via SNMP, all unauthenticated and from the internet. What was going on?
The router that Gerry and Eric were testing had the following SNMP and ACL configuration in place:
snmp-server community OURCOMMUNITY RO SNMP_ALLOWED
snmp-server ifindex persist
ip access-list standard SNMP_ALLOWED
permit x.x.x.0 0.0.0.255
Although the SNMP v2 server was properly restricted and SNMP v3 was not explicitly configured, the SNMP v3 service was still leaking information about the device via unauthenticated requests from the internet.
SNMP is known to be a common weak point in device security. Default, guessible, and hardcoded SNMP communities expose information and management capabilities to the network at large. The lack of encryption in SNMP v1 and v2 allow attackers to capture credentials sent by management tools. Attackers can abuse the weak security of one device to obtain sensitive information about other systems on the network.
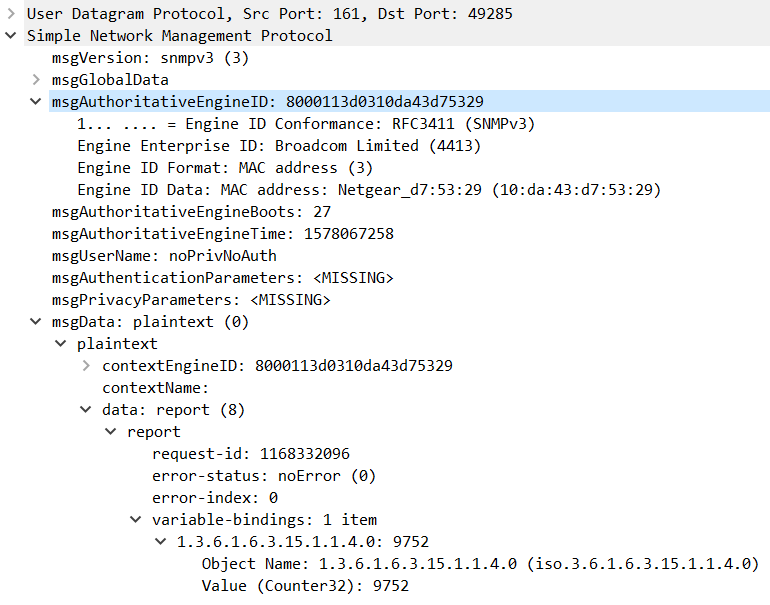
These concerns led to the development of SNMP v3, which introduces encryption, strong authentication, and message integrity. SNMP v3 has been the official version of the protocol since 2004, but still holds a few surprises when it comes to information exposure. To successfully authenticate over SNMP v3, the client device needs the EngineID of the server, and obtains this by sending a minimal SNMP v3 request. The response includes both the Authoritative EngineID and the Context EngineID:
These EngineID values expose a vendor name and often, the MAC address of the device. The MAC address in turn can be used to identify the vendor and manufacturing date of the device (via mac-ages). runZero will also correlate the MAC address across the scan scope, linking all responsive IP addresses to the same asset using this technique. The EngineBoots, EngineTime, and the usmStatsUnknownEngineIDs counter (the final reported value) can be useful to an attacker are well.
Preventing this exposure requires explicit ACLs on the external interfaces. Gerry and Eric were able to stop this information leak by applying a UDP ACL on port 161. No changes were needed to the existing SNMP v2 configuration.
ip access-list extended INTERNET_IN
deny udp any x.x.x.0 0.0.0.255 eq snmp
In cases where SNMP v3 over TCP is used, additional ACL lines may be necessary to completely block access to the SNMP v3 service. If you find this stuff interesting, you might like our recent talk on Modern Network Discovery, which covers the SNMP v3 information leaks (slide 25) among other methods used by runZero to discover and enumerate network devices.
Thanks again to Gerry Gosselin and Eric Rioux of VertitechIT for reaching out about this issue, identifying the root cause, and sharing their notes!
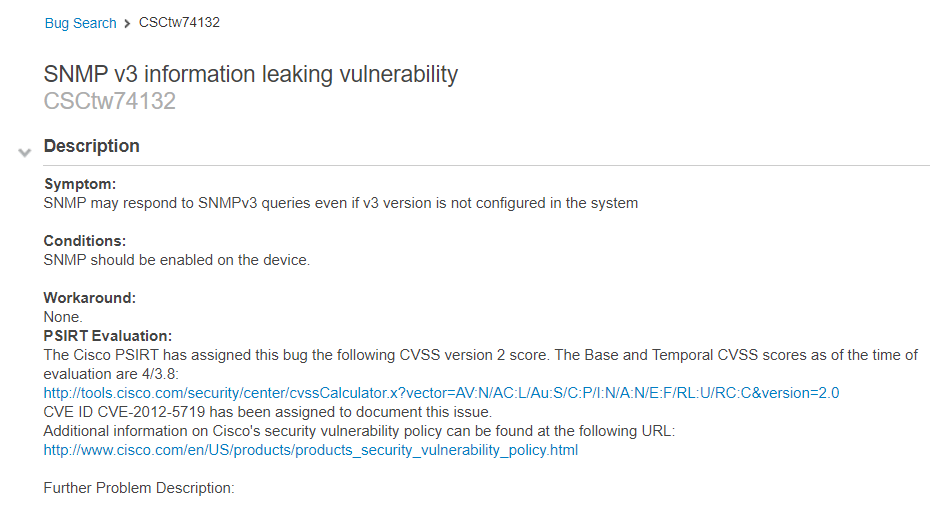
Update: It appears that Cisco bug CSCtw74132 ("SNMP v3 information leaking vulnerability" April 18, 2019) may be the root cause and may apply to a wider range of products than initially thought:
-HD