Josh Lucas, a cybersecurity engineer at Loop Secure, recently took first place in Microsoft’s Sentinel Hackathon for his submission, "[runZero]" Network Discovery solution for Microsoft Sentinel.” For his project, Josh was looking for a way to better enable security teams during incident response, so he designed his solution to include “information that isn't readily available from other solutions.” Josh achieved this by supplementing Microsoft Sentinel with two key runZero strengths: asset discovery and custom integrations.
Microsoft’s Ann Johnson, Corporate Vice President of Security, Compliance & Identity (SCI) Business Development, shared the following on Josh’s win:
"Today’s threat landscape requires that customers deploy intelligent solutions at speed and scale. The [runZero] Network Discovery solution offers deep Microsoft Sentinel integration with rich analytics, providing customers with new capabilities and enabling them to realize value faster. Its completeness makes the solution a standout amongst the hackathon competition."
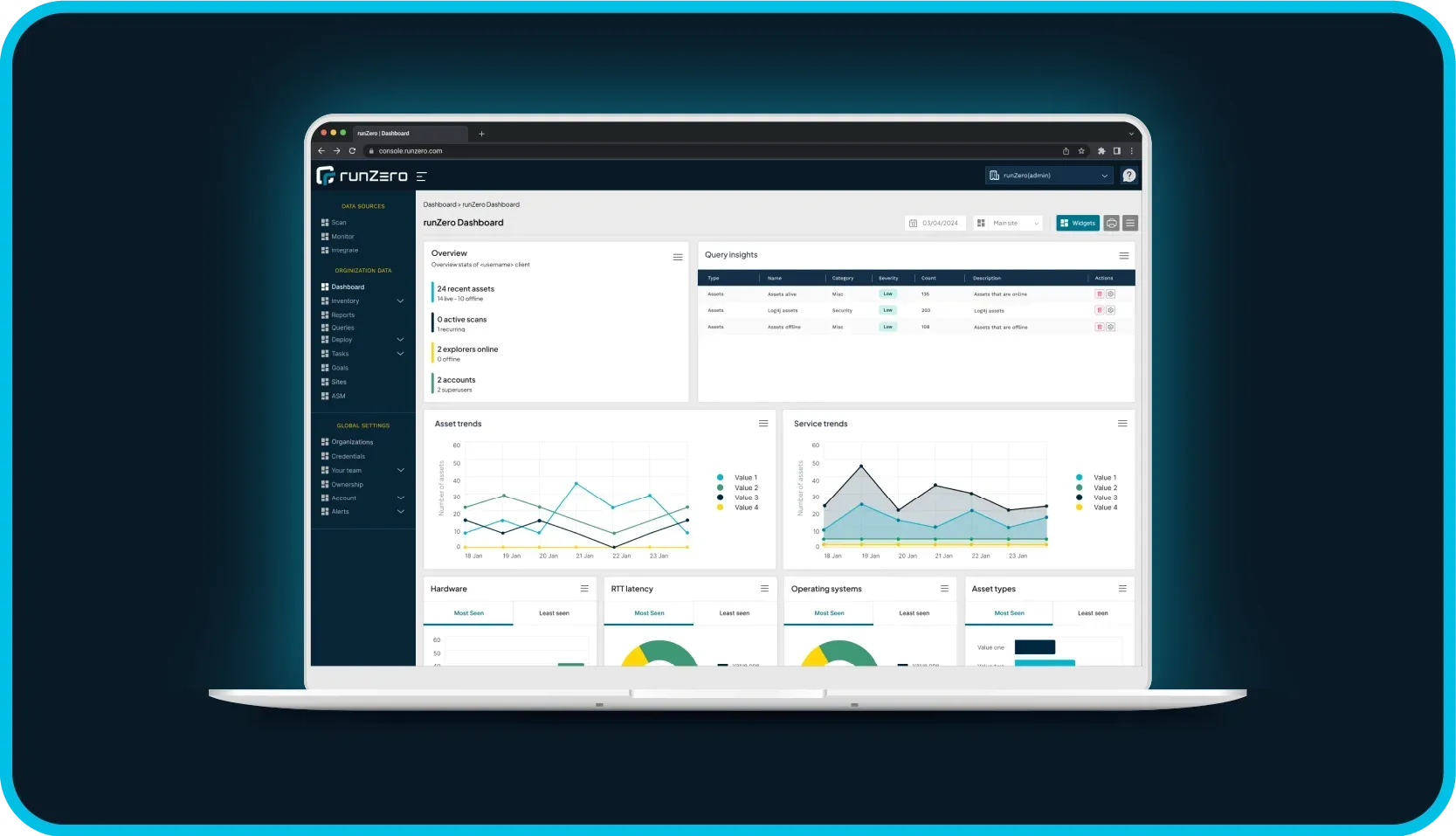
Here at runZero, we are very excited to hear of Josh’s winning submission! Congrats, Josh! Let's take a look at the runZero capabilities he used (and a few other runZero capabilities, as well). Hopefully, you'll find some inspiration for your next project or solution.
Design overview #
Josh authored a very detailed writeup (and video), including a link to all the pieces you need to recreate his project. The following is a simplified diagram of his solution:
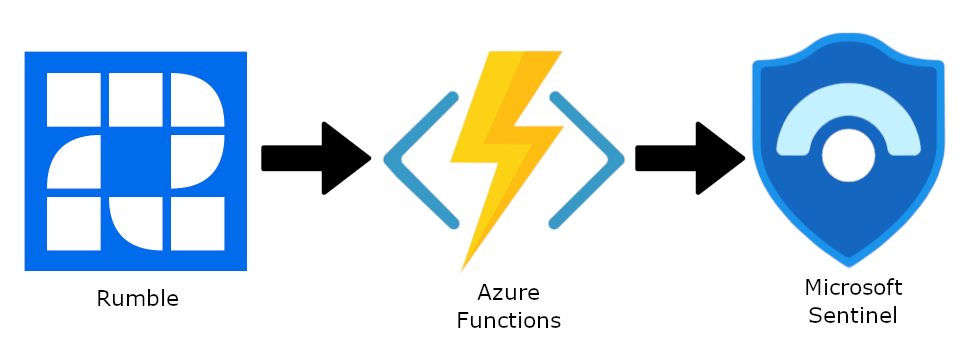
Illustrated above, Josh’s solution utilizes a custom integration with the runZero API and Rules Engine to send runZero asset and service inventory data to Microsoft Sentinel (via Azure Functions). In addition to custom integration support, runZero also offers a number of ready-to-use integrations.
Best-in-class asset discovery #
The runZero Explorer is a lightweight scan engine that can be easily deployed and scheduled to perform network scans, including recurring scans. Network assets discovered via these scans will populate into the asset inventory, creating new entries for first-time-seen assets, updating existing entries for previously-seen assets, and marking assets no longer seen as “offline.” Each asset is fingerprinted to provide as much data and context as possible about a particular asset, including the type of asset, vendor, and operating system. Fingerprinting is also performed for each discovered service running on an asset, including protocol, product, and vendor.
Josh’s project relies on runZero for asset and service discovery, which feeds detailed inventory data into Microsoft Sentinel to “enrich hunting queries with contextual network information and provide insights.”
Pulling asset service inventory via the runZero API #
The runZero REST API offers robust support for custom integrations. You can do things like pull asset and service data, manage scans, manage account settings, and much more. To see what you can do, check out all of the available runZero API endpoint details in our Swagger documentation.
For his project, Josh utilizes the runZero API to populate runZero-discovered asset and service inventory data into Sentinel (via Azure Functions).
Webhooks via rules #
The runZero Rules Engine is a highly configurable feature. It provides the ability to automatically detect conditions and events, such as account logins, scan completions, and changes in inventory. Additionally, you can specify an action to automatically trigger based on certain conditions and events, like tagging certain assets following a scan or sending an alert if a high-value asset wasn't found.
Josh’s project uses the runZero Rules Engine to determine when new assets have been discovered (“new-assets-found”) or existing assets have changed (“assets-changed”), and he automatically forwards appropriate details via webhook to Azure Functions, which updates Sentinel with the latest data.
But wait, there’s more! #
Not ready to build your own custom integrations? Take a look at runZero's ready-to-use integrations. runZero regularly adds new integrations, so keep checking back to see what's new.